Advanced Protection with Centralized Security Management
- Vishal Masih
- Feb 26
- 4 min read
In today’s fast-paced digital world, security threats are evolving faster than ever. Organizations face a constant barrage of cyberattacks, data breaches, and compliance challenges. So, how do you keep your defenses strong without drowning in complexity? The answer lies in centralized security management. It’s a game-changer that simplifies your security landscape, making it easier to protect your assets and respond to threats quickly.
Let me walk you through why centralized security management is essential, how it works, and how it can transform your cybersecurity strategy.
Why Centralized Security Management Matters
Imagine juggling multiple security tools, each with its own dashboard, alerts, and policies. It’s overwhelming, right? Centralized security management brings all those tools under one roof. This means you get a single pane of glass to monitor, control, and respond to security events.
Here’s why that’s a big deal:
Faster response times: When everything is connected, spotting and reacting to threats happens in real-time.
Reduced complexity: No more switching between different systems or struggling to correlate data.
Improved visibility: You get a comprehensive view of your entire security posture.
Consistent policies: Apply security rules uniformly across your network, endpoints, and cloud environments.
For organizations handling sensitive data or operating in regulated industries, this approach isn’t just convenient—it’s critical.

How Centralized Security Management Works
At its core, centralized security management integrates various security components into a unified platform. Think of it as the command center for your cybersecurity efforts. Here’s a step-by-step look at how it typically functions:
Data Collection: Security devices and software—firewalls, intrusion detection systems, endpoint protection, cloud security tools—send logs and alerts to the central platform.
Data Aggregation and Correlation: The platform aggregates this data and uses analytics to identify patterns or anomalies that could indicate a threat.
Alert Prioritization: Not all alerts are created equal. The system prioritizes them based on severity and potential impact.
Automated Response: Some platforms can automatically isolate affected systems, block malicious IPs, or trigger other defensive actions.
Reporting and Compliance: Generate detailed reports to meet regulatory requirements and inform stakeholders.
This streamlined process helps security teams stay ahead of threats without getting bogged down in noise.
The Role of Managed Security Solutions
Now, you might be wondering, “Can I handle this in-house?” Sure, but it’s not always practical. That’s where managed security solutions come into play. These services provide expert monitoring and management of your security environment 24/7.
Here’s what makes managed security solutions so valuable:
Expertise on demand: Access to seasoned security professionals without hiring full-time staff.
Cost efficiency: Avoid the expense of building and maintaining your own security operations center.
Scalability: Easily adjust services as your organization grows or your needs change.
Advanced tools: Benefit from cutting-edge technology that might be out of reach otherwise.
By partnering with a trusted provider, you gain peace of mind knowing your defenses are always active and evolving.

Practical Steps to Implement Centralized Security Management
Ready to take the plunge? Here’s a straightforward roadmap to get started:
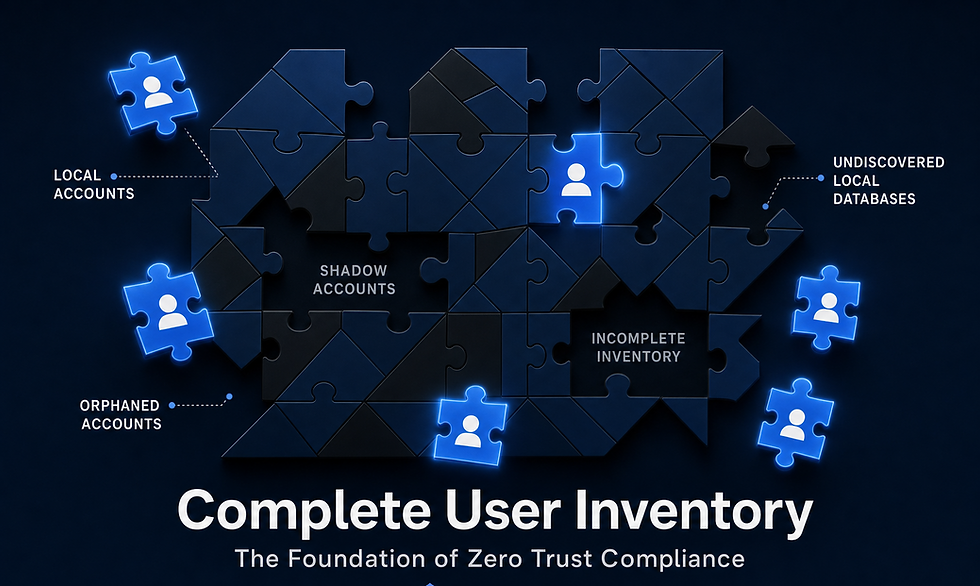
Assess Your Current Security Landscape
Identify all existing security tools, processes, and gaps. This baseline helps you understand what needs integration.
Choose the Right Platform
Look for solutions that support your environment—whether on-premises, cloud, or hybrid—and offer scalability.
Integrate Your Security Tools
Connect firewalls, endpoint protection, SIEM (Security Information and Event Management), and other systems to the centralized platform.
Define Clear Policies and Procedures
Establish consistent rules for threat detection, response, and reporting.
Train Your Team
Ensure your security staff understands how to use the platform effectively and interpret alerts.
Consider Managed Services
If resources are tight, explore managed security solutions to augment your team.
Continuously Monitor and Improve
Cybersecurity is not a set-it-and-forget-it task. Regularly review performance and update your defenses.
Following these steps will help you build a robust, manageable security framework.
Benefits Beyond Security: Saving Time and Money
Centralized security management isn’t just about stopping attacks. It also helps organizations save valuable time and money. Here’s how:
Reduced operational costs: Fewer tools and less manual work mean lower expenses.
Streamlined compliance: Automated reporting simplifies audits and regulatory adherence.
Improved productivity: Security teams spend less time chasing false alarms and more time on strategic initiatives.
Faster incident resolution: Quicker detection and response minimize downtime and damage.
In short, it’s an investment that pays off by making your security smarter and your operations leaner.
Looking Ahead: Building a Resilient Security Future
The cybersecurity landscape will keep changing. Threats will grow more sophisticated, and regulations will evolve. That’s why adopting centralized security management is a forward-thinking move. It sets the foundation for agility and resilience.
By simplifying complex systems, consolidating tools, and automating processes, you position your organization to face whatever comes next with confidence. And if you ever feel overwhelmed, remember that expert partners are ready to help you navigate this journey.
Security doesn’t have to be complicated. With the right approach, it can be your strongest asset.
If you want to explore how centralized security management and managed security solutions can work for your organization, don’t hesitate to reach out. Let’s make cybersecurity simpler, smarter, and more effective together.



Comments