Protect Your Devices with Device Cybersecurity Solutions
- Vishal Masih
- Feb 25
- 4 min read
In today’s fast-paced digital world, protecting your devices is no longer optional. Every organization, whether a federal agency, a Fortune 100 company, or a non-profit, faces constant threats from cybercriminals. These threats can disrupt operations, steal sensitive data, and damage reputations. That’s why investing in device cybersecurity solutions is crucial. Let’s dive into how you can safeguard your devices effectively and keep your organization secure.
Why Device Cybersecurity Solutions Matter
You might wonder, "Why should I care about device cybersecurity solutions?" Well, think about it. Every device connected to your network is a potential entry point for cyberattacks. Laptops, smartphones, tablets, and even IoT devices can be exploited if left unprotected.
Here’s the reality: cyber threats are evolving rapidly. Hackers use sophisticated methods like ransomware, phishing, and zero-day exploits to breach defenses. Without proper protection, your devices become vulnerable targets.
Device cybersecurity solutions help by:
Detecting and blocking malware before it can cause harm
Monitoring device activity for suspicious behavior
Enforcing security policies across all endpoints
Providing real-time alerts and automated responses
By implementing these solutions, you reduce the risk of data breaches and downtime, saving your organization time and money.

Key Features to Look for in Device Cybersecurity Solutions
Not all cybersecurity tools are created equal. When choosing device cybersecurity solutions, focus on features that provide comprehensive protection without complicating your IT environment.
Here are some must-have features:
Antivirus and Anti-malware Protection
This is your first line of defense. It scans files and programs to detect and remove malicious software.
Firewall and Network Security
Controls incoming and outgoing network traffic to prevent unauthorized access.
Endpoint Detection and Response (EDR)
Continuously monitors endpoints to detect suspicious activities and respond quickly.
Data Encryption
Protects sensitive information stored on devices by converting it into unreadable code.
Patch Management
Automatically updates software to fix vulnerabilities before hackers can exploit them.
User Access Controls
Limits device access based on user roles, reducing the risk of insider threats.
Cloud Integration
Enables centralized management and scalability, especially important for organizations with remote or hybrid workforces.
When these features work together, they create a robust shield around your devices.
How to Implement Device Cybersecurity Solutions Effectively
Implementing cybersecurity solutions can seem daunting, but breaking it down into clear steps makes it manageable. Here’s a straightforward approach:
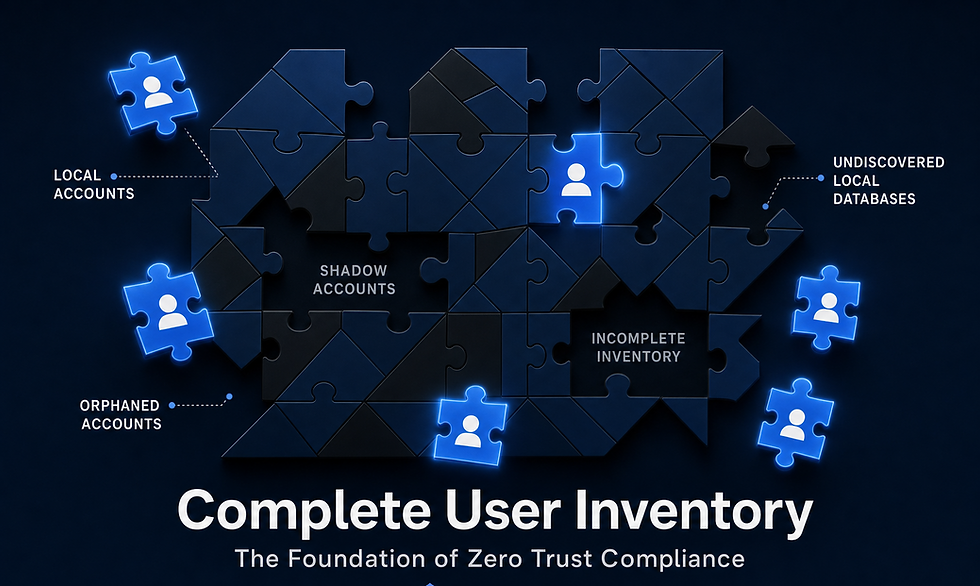
Step 1: Assess Your Current Security Posture
Start by identifying all devices connected to your network. Conduct a risk assessment to understand vulnerabilities and prioritize which devices need immediate attention.
Step 2: Choose the Right Solution
Select a solution that fits your organization’s size, industry, and specific security needs. Look for vendors with proven track records and strong customer support.
Step 3: Develop a Security Policy
Create clear guidelines for device usage, password management, software updates, and incident reporting. Make sure everyone in your organization understands and follows these policies.
Step 4: Deploy the Solution
Roll out the cybersecurity tools across all devices. Use automated deployment tools to save time and ensure consistency.
Step 5: Train Your Team
Educate employees about cybersecurity best practices. Human error is often the weakest link, so awareness is key.
Step 6: Monitor and Update Regularly
Cyber threats evolve, so your defenses must too. Continuously monitor device activity and apply updates promptly.
By following these steps, you’ll build a strong defense that adapts to new challenges.

The Role of Automation in Device Cybersecurity Solutions
Automation is a game-changer in cybersecurity. It helps organizations like yours stay ahead of threats without overwhelming IT teams.
Here’s how automation enhances device cybersecurity:
Automated Threat Detection
AI-powered tools can identify unusual patterns and flag potential attacks instantly.
Automatic Patch Deployment
Ensures devices are always up to date without manual intervention.
Incident Response Automation
Quickly isolates infected devices and initiates remediation steps to minimize damage.
Simplified Compliance Reporting
Automatically generates reports to meet regulatory requirements.
Automation reduces human error, speeds up response times, and frees up your security team to focus on strategic tasks. It’s a smart way to simplify complex systems and consolidate tools, aligning perfectly with the goal of saving time and money.
Why Partnering with Experts Makes a Difference
You don’t have to go it alone. Partnering with a trusted cybersecurity provider can make all the difference. Experts bring deep knowledge, experience, and resources that help you:
Choose the best device cybersecurity solutions for your unique needs
Customize security policies and workflows
Implement and manage solutions efficiently
Stay updated on the latest threats and compliance standards
For example, Zephon LLC specializes in simplifying complex cybersecurity systems, consolidating tools, and automating processes. Their approach helps organizations achieve peace of mind while optimizing security investments.
If you want to explore reliable endpoint protection solutions that fit your organization, working with a partner like Zephon can be a game-changer.
Taking the Next Step Toward Stronger Device Security
Securing your devices is an ongoing journey, not a one-time fix. Start by evaluating your current defenses and identifying gaps. Then, invest in comprehensive device cybersecurity solutions that offer layered protection.
Remember, the goal is to create a seamless security environment that protects your data, supports your operations, and adapts to evolving threats. With the right tools, policies, and partnerships, you can achieve this balance.
Don’t wait for a cyberattack to expose vulnerabilities. Take proactive steps today to protect your devices and safeguard your organization’s future.
By focusing on practical, actionable strategies and leveraging expert partnerships, you’ll be well on your way to a stronger cybersecurity posture. Stay vigilant, stay informed, and keep your devices secure.



Comments